Custom User Folder Access
This documents the folder access needed if one chooses not to use the local system user and instead configures SpinFire Manage services with a custom user. The table below summarizes the permissions required, followed by details for each.
WebApp |
PipelineService |
|
C:\ProgramData\SpinFire\SpinFire Manage |
R/W |
R/W |
CatalogStorageLocation |
R/W |
|
C:\inetpub\wwwroot\Centro |
R/W |
|
C:\Program Files\SpinFire\SpinFire Manage |
R/W |
|
C:\ProgramData\SpinFire\SpinFire Insight |
R (for health checks) |
|
TempFolderLocation (if configured) |
R/W |
R/W |
Folder access required by SpinFire Manage services
To ensure SpinFire Manage and its components operate correctly, verify and set folder permissions in the areas described below.
ProgramData Folder
Both services (WebApp and PipelineService) require R/W access to C:\ProgramData\SpinFire\SpinFire Manage for internal storage (e.g. ShapeSearch index, pipeline databases, logs, etc.).
The WebApp also requires access to the CatalogStorageLocation. This resides inside the WebApp installation folder by default so it is granted automatically, but if it is changed or if the ApplicationPool user is changed, it may need to be adjusted.
Installation Location
Each service requires access to its own install location. This is granted automatically at install time, but if the user that the service runs under is changed, access for that user must be explicitly granted to the respective install locations:
C:\inetpub\wwwroot\Centro (WebApp)
C:\Program Files\SpinFire\SpinFire Manage (PipelineService)
Temp Folder
Both services may require access to the folder specified by TempFolderLocation in appSettings.jsonc. The default value is temp, which resolves to C:\ProgramData\SpinFire\SpinFire Manage\temp — implicitly covered by the ProgramData folder permission above.
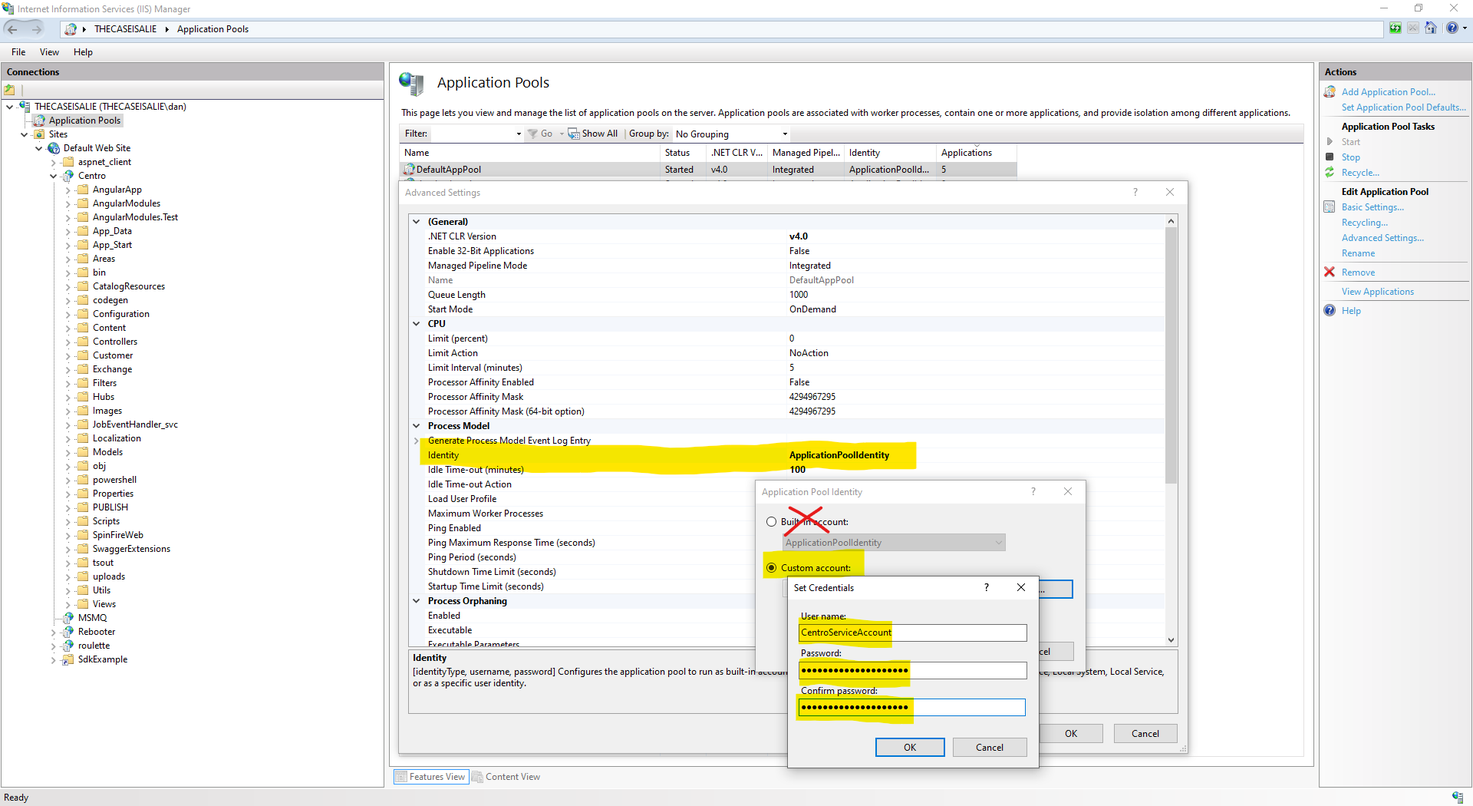
The easiest approach is to run both services under the same service account user and grant R/W access to C:\ProgramData\SpinFire\SpinFire Manage for that user. The WebApp runs under an IIS Application Pool, which can be configured to impersonate the same service account: